Gain Visibility. Take Control.
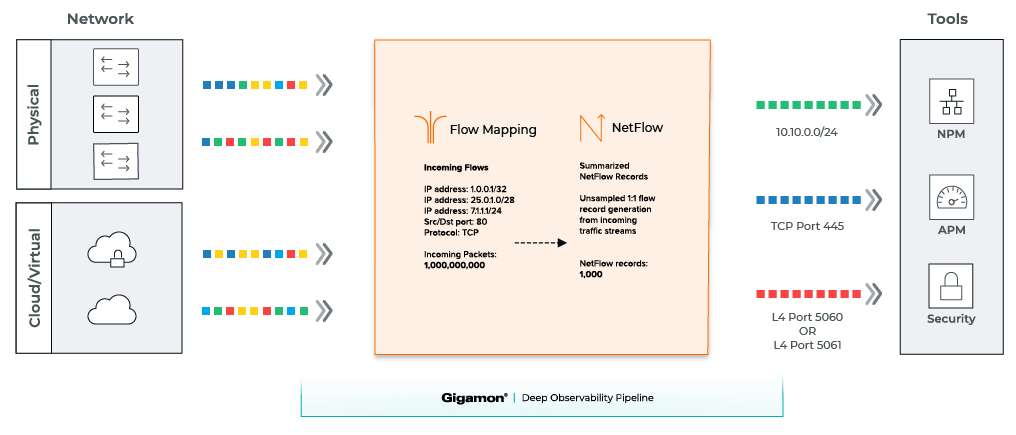
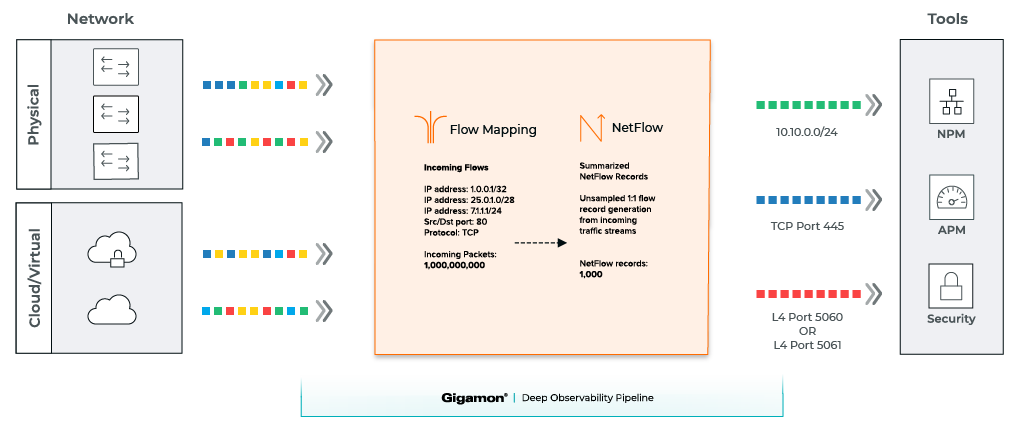
NetFlow is an efficient method for delivering basic Layer 2–4 network traffic data to analysis tools. But extracting high-quality NetFlow using routers and switches can severely strain resources, leading to dropped packets. Other problems include reduced accuracy by relying on sampling and restricted interoperability due to limited format options.
The GigaSMART® NetFlow module overcomes these roadblocks by automatically generating NetFlow records and exporting them to your SIEMS, storage platforms and other tools. NetFlow from Gigamon has these advantages:
- Offloads NetFlow generation load from routers and switches
- Provides full fidelity NetFlow intelligence vs. information derived from sampled packets
- Supports all formats, including IPFIX and CEF
Gigamon NetFlow provides network and security teams with visibility into traffic types across systems, including multi-cloud environments. This helps organizations catch denial of service attacks, data exfiltration and other security-related activities. Similarly, network- and application-performance management (NPM and APM) tools can quickly troubleshoot and remediate user experience concerns and ensure SLAs.
Want to take NetFlow to the next level?
Expand your metadata choices to over 5,000 attributes and obtain Layer 7 insights. These include details on hundreds of social media, database, ICS, financial and many other types of applications. Find out how using Gigamon Application Metadata Intelligence.
Reduce Time to Threat Detection
NetFlow Generation
Gigamon Deep Observability Pipeline
GigaSMART Features
GigaSMART® offers several essential traffic intelligence services required for deep observability into infrastructure blind spots.
NetFlow Generation
Delivers basic Layer 2–4 network traffic data to analysis tools.
Source Port Labeling
Provides context to packets and identifies behaviors and threats based on network location.
Adaptive Packet Filtering
Identifies patterns across any part of the network packet, including the packet payload.
De-duplication
Targets, identifies, and eliminates duplicate packets, blocking unnecessary duplication and sending optimized flows.
Packet Slicing
Truncates packets while preserving the protocol headers required for network analysis.
Advanced Load Balancing
Divides and distributes traffic among multiple tools based on a variety of data points.
Advanced Flow Slicing
Reduces bandwidth usage by slicing payloads and packets from long data flows.
Masking
Provides customizable data protection by overwriting specific packet fields with a set pattern.
Tunneling
Alleviates blindness of business-critical traffic at remote sites, virtualized data centers, or in the public or private cloud.
Application Visualization
Provides a complete view of the applications running on your network.
Application Filtering Intelligence
Extends Layer 7 visibility to thousands of common and proprietary applications.
Application Metadata Intelligence
Provides application visibility to identify performance and quality issues, and potential security risks.
GTP Correlation
Enables mobile service providers to monitor subscriber data in GPRS Tunneling Protocol tunnels.
FlowVUE Flow Sampling
Provides subscriber IP-based flow sampling.
5G Correlation
Forwards subscriber sessions to specific tools by filtering on subscriber, user device, RAN, or network slice IDs.
SSL/TLS Decryption
Creates a secure channel between the server and the end user's computer or other devices as they exchange information.
“With the deep observability that Gigamon provides, we’re gaining access to all traffic across our infrastructure and amplifying the power and fidelity of our networks.”
“Any equipment can see source and destination, but inside the packet is what matters. Now we’re able to get a lot more visibility into the packet. We also observe more east-west traffic”
Have Questions?
We're here to help you find the right solution for your business.
By submitting this form, you agree to our Terms & Agreement. View our Privacy Statement.