Assure Cloud Security and Compliance
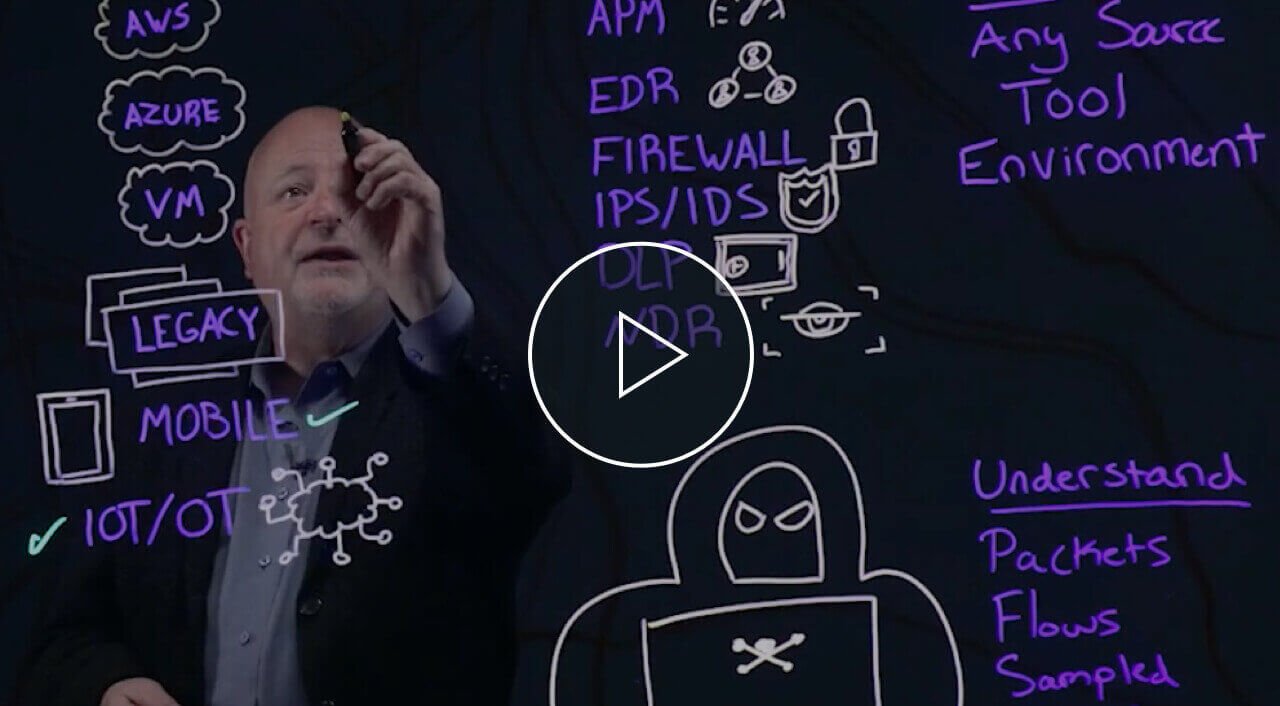
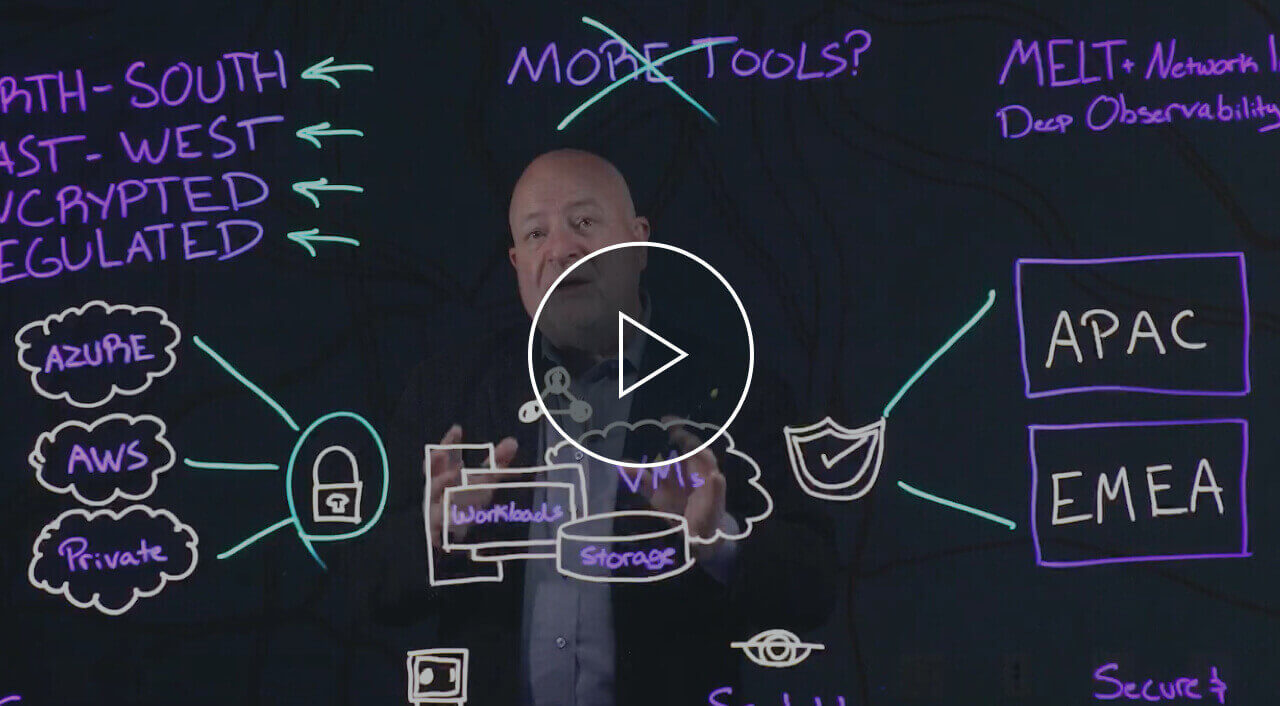
GigaVUE Cloud Suite™ enables seamless migration of security and compliance practices to hybrid cloud environments. It provides complete visibility into all North-South and lateral East-West traffic and masks confidential data in motion across the cloud.
When combined with cloud-native security capabilities, the packet and metadata-level visibility provides a solid Zero Trust foundation.
- Enhance cloud-native security capabilities with packet and metadata-level insights for precise threat detection
- Filter and route cloud traffic to existing security tools, extending your security posture to the cloud and maximizing the ROI of these tools
- Leverage application metadata to gain context and insights to detect and respond to application-level threats
- Gain more situational awareness with GigaVUE® Enriched Metadata for Cloud Workloads for faster troubleshooting, threat detection, and incident response
How Gigamon Can Help
GigaVUE Cloud Suite ensures your security and compliance posture can scale to hybrid and multi-cloud architectures and provides the visibility necessary to build a zero trust security architecture.
Secure virtual traffic
Containers are a critical cloud technology, but they pose new challenges; maintain in-depth visibility into your containerized traffic with GigaVUE Cloud Suite.
Scalable elastic visibility
Visibility must increase as your workloads scale up and scale out; GigaVUE Cloud Suite provides complete visibility into both North-South and East-West traffic.
Get to Zero Trust faster
GigaVUE Cloud Suite aligns to NIST and SANS guidelines to provide the visibility you need to make zero trust a reality, today.
"With Gigamon, PT KAI has gained deep observability into risk and threat telemetry, and seamlessly integrated with our security tools, enabling informed decision-making and improved compliance."

“We’re excited about the new Universal Container Tap (UCT) solution in GigaVUE Cloud Suite as it shows how Gigamon continues to innovate to stay current with modern software architectures, including a wide range of Kubernetes-based container deployments.”

“Organizations are turning to deep observability to regain end-to-end insight into AI-driven data flows, strengthening security, improving performance, and enabling greater automation. As the fastest-growing segment we cover, deep observability is emerging as a critical data layer that delivers consistent, high-quality network intelligence to AI-driven systems and helps organizations realize and protect the value of their AI investments.”
Resources
Gigamon Deep Observability Pipeline
Lockheed Martin Enhances Cloud Visibility
Frost & Sullivan
Request a Live Cloud Demo
Ready to see the Gigamon Cloud Solution in action? Schedule a live demo and learn how Cloud Suite provides complete visibility into the cloud, to help you accelerate your cloud migration.