What Is Application Intelligence?
Application intelligence is the power to identify, filter, and enrich application data coming from your hybrid cloud. It directs precise application and metadata flows to security and observability tools for insight into:
- Shadow IT and other unauthorized activities
- Anomalous application or user behavior
- Potential user experience issues
Gigamon Application Intelligence gives NetOps, CloudOps, and security teams full visibility into applications running in datacenters and public clouds. Therefore, you can maintain consistently strong security across your environment plus get to the root causes of vulnerabilities and performance bottlenecks.
Application Visualization
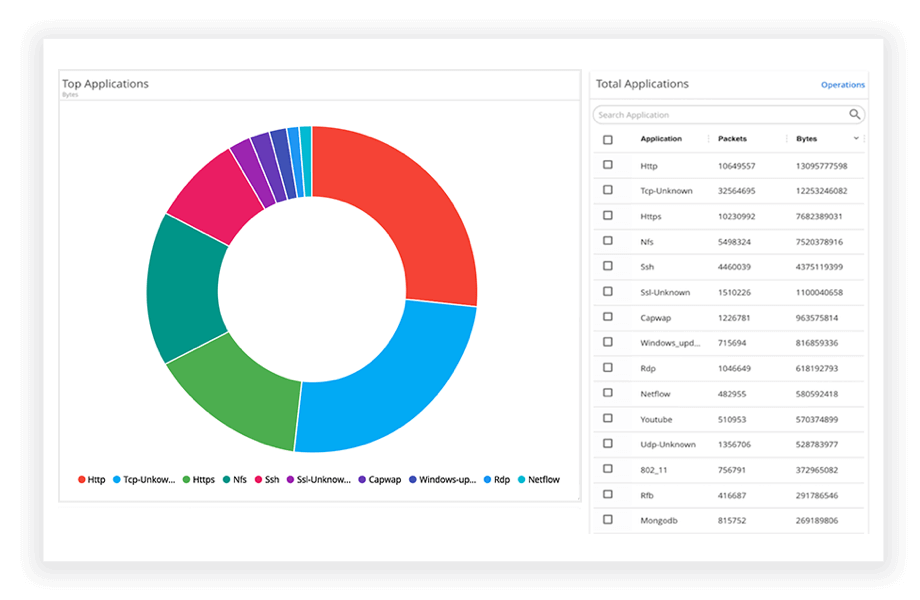
Application visualization, a feature of Application Filtering Intelligence and Application Metadata Intelligence, leverages deep packet inspection to identify over 3,500 common and proprietary applications and share this information with your tools. Drill down to see application usage, patterns, and network resource consumption.
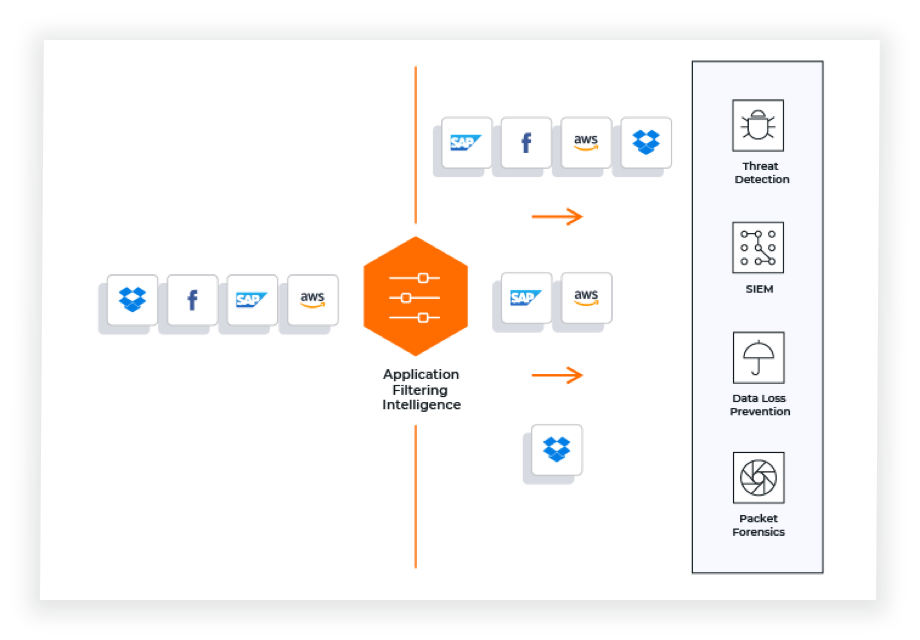
Application Filtering Intelligence
Application Filtering Intelligence (AFI) directs traffic by application or application family to the appropriate tools for over 3,500 apps. Using simple flow control, pass specific traffic or drop irrelevant application traffic to your tools, saving storage and processing resources. Use cases show AFI can increase efficiency and capacity by up to 80 percent.
Application Metadata Intelligence
Application Metadata Intelligence (AMI) generates rich contextual information about your applications and protocols that you can send to your security and observability tools for analysis. Using deep packet inspection, AMI extracts and summarizes data from 7,000+ attributes spanning over 3,500 apps. Empower tools to rapidly spot suspicious activities and performance issues.
Put Gigamon Application Intelligence to Work
Application Intelligence Benefits
Application Intelligence technology empowers your business with a deep and detailed view of application data within your network.
- Automatically visualize thousands of applications running on your network
- Drill down into individual applications, application components, and protocols to understand the sources of performance bottlenecks or security vulnerabilities
- Drive network and tool efficiency by sending only relevant application traffic to the appropriate tools for analysis
- Deliver detailed context needed for security teams and analytics tools to do their jobs quickly and accurately
Managing and Securing DX Applications
Accelerate your digital transformation journey by giving teams and tools the intelligent application visibility needed to monitor and secure modern digital applications.
- Isolate and extract application and component traffic across multiple tiers for monitoring
- Provide intelligent application metadata to analytics tools, enabling faster detection of customer experience, application performance, and security-related issues
- Send only relevant traffic to the appropriate tools to reduce load and increase effectiveness
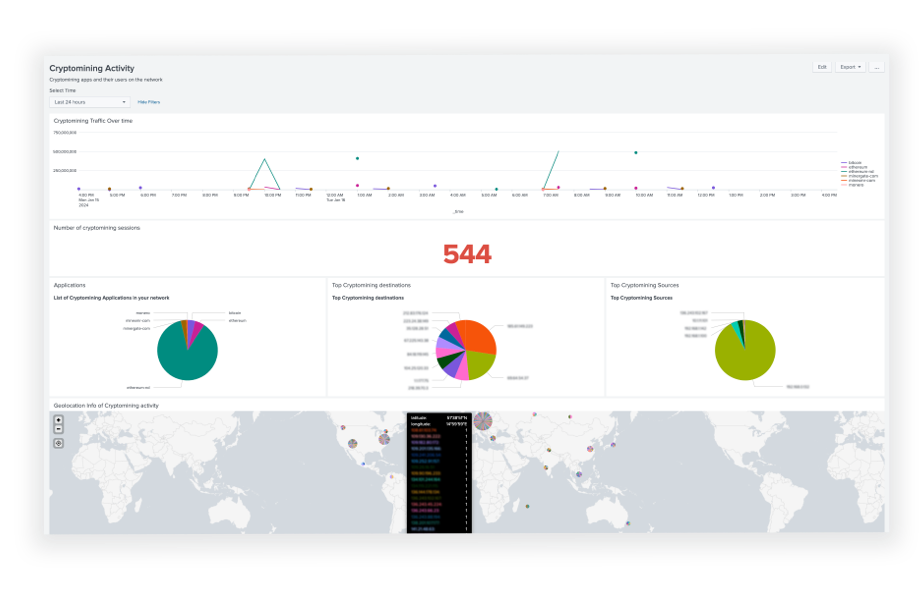
Detecting and Remediating Threats
With Application Intelligence, security tools are armed with more of the right data to perform their functions. You benefit from faster detection, isolation, and remediation of threats and noncompliant activities.
- Provide contextual data to help tools detect threats, such as lateral movements of malware
- Impede port spoofing attacks by precisely identifying app traffic via deep packet inspection
- Shine a light on shadow IT by revealing hidden and unauthorized applications
Improving Tool Efficiency and Performance
The growing volume of application traffic can overwhelm network and security tools, impacting tool performance and effectiveness. Application Intelligence helps your tool ecosystem run more efficiently.
- Extract irrelevant application traffic before it’s sent to tools, saving storage and processing resources
- Focus teams and tools on mission-critical applications that warrant extra scrutiny
- Feed granular application performance and behavior data to analytics tools, helping IT teams quickly find and fix performance issues
Seeing Through the Clouds to the Journey Ahead
Application Intelligence
Gaining Control of Complex DX Apps
“Evolving customer expectations are driving many of our digital initiatives. Having complete visibility into the performance and security of our digital applications is key to delivering on the expectations of user experience and trust our customers demand.”